Enhancing Cyber Security through Advanced Data Destruction Techniques
Checking Out the Relevance of Information Destruction in the Context of Computer Safety Providers and Protecting Confidential Information
In an age where data violations are increasingly common, the relevance of effective information devastation can not be overstated. What techniques can organizations implement to boost their information destruction protocols?
Understanding Information Devastation
Information damage is a crucial component of computer protection that includes the permanent elimination of data from storage gadgets to avoid unapproved gain access to and possible information violations. In an increasingly digital landscape, companies face enhanced threats connected with delicate details being incorrectly accessed or manipulated. Reliable information destruction safeguards versus these hazards, making certain that private dataâEUR" such as client details, copyright, and monetary recordsâEUR" can not be recouped after disposal.
Recognizing the significance of information damage expands beyond simple conformity with regulatory and legal frameworks; it is vital for maintaining organizational honesty and trust. When information is incorrectly managed or improperly destroyed, the repercussions can be extreme, consisting of financial loss, reputational damages, and legal liabilities.
Techniques of Information Obliteration

One common method is information wiping, which includes overwriting existing data with arbitrary patterns multiple times. This method makes the initial data irretrievable, making it a preferred choice for organizations seeking to shield secret information.
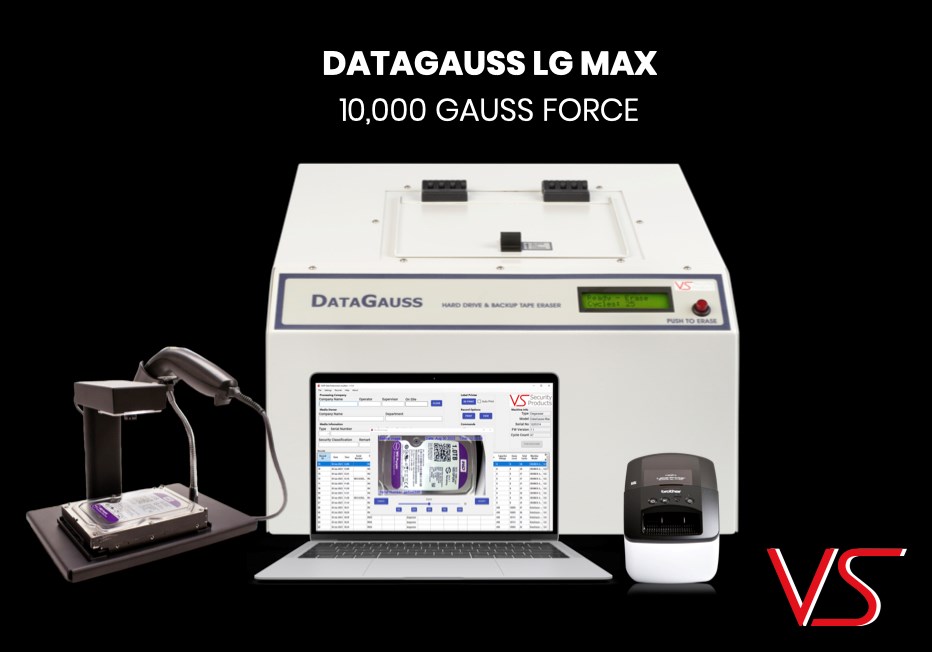
An additional method is degaussing, which utilizes a powerful electromagnetic field to interrupt the magnetic domains on storage space tools, successfully erasing the data. This strategy is particularly effective for magnetic media yet is not suitable to solid-state drives.
Physical destruction is one more robust approach, including the shredding or crushing of storage space gadgets. This approach warranties that information healing is essentially difficult, making it ideal for very sensitive information.
Finally, security can work as a complementary approach to data eradication. By securing data before deletion, organizations can include an extra layer of safety and security, ensuring that even if remnants are recouped, they remain hard to reach without the decryption secret. Each method needs to be selected based upon the level of information level of sensitivity and the details safety requirements of the company.
Legal Conformity and Information Protection
Organizations have to navigate an intricate landscape of legal requirements connected to information safety and security, specifically after executing methods of data elimination. Different guidelines, such as the General Data Protection Law (GDPR) and the Medical Insurance Mobility and Accountability Act (HIPAA), enforce strict standards on how organizations should get rid of and handle of delicate information. Failing to adhere to these guidelines can result in substantial legal effects, consisting of considerable penalties and reputational damages.
Information devastation procedures should be carefully recorded to demonstrate conformity with appropriate legislations and standards. This documentation not only works as proof of adherence to legal commitments however also highlights a dedication to protecting sensitive info. Organizations needs to additionally establish clear plans pertaining to data retention and devastation timelines, making sure that data is not held longer than required.

Additionally, normal audits and assessments of information destruction methods are important to preserve compliance and adapt to advancing lawful frameworks (data destruction). By proactively addressing legal demands, organizations can minimize dangers connected with data violations and demonstrate their commitment to information security. Inevitably, prioritizing lawful conformity in information destruction procedures is not just a regulatory responsibility, yet a fundamental aspect of a robust information safety technique
Influence On Business Reputation
The reputation of a service can be significantly impacted by its technique to information devastation and monitoring. In today's electronic landscape, where information breaches can happen anytime, the failing to properly take care of sensitive info can cause extreme effects. Organizations that improperly handle data damage danger subjecting personal consumer info, which not just violates personal privacy regulations however likewise wears down trust fund amongst customers and stakeholders.
A ruined credibility can lead to reduced client commitment, as clients end up being reluctant to involve with a business that has actually shown oversight in protecting their information. Furthermore, adverse attention bordering an information breach can have an enduring impact, as possible customers may be deterred by the viewed absence of security. This can result in a direct decrease in income and market share.
Moreover, organizations that prioritize information destruction as part of their security method can enhance their credibility by showcasing their dedication to protecting delicate information. By embracing stringent data monitoring practices, organizations can not only mitigate risks yet additionally place themselves as credible entities in my latest blog post their particular industries, thus reinforcing their total brand name photo.

Best Practices for Secure Disposal
Applying best techniques for safe disposal of information is vital for mitigating threats connected with information violations and ensuring compliance with personal privacy guidelines. Organizations must adopt a thorough data disposal plan that outlines procedures for both physical and digital data damage.
For physical data storage gadgets, such as disk drives, shredding or degaussing is recommended to prevent information healing. Additionally, organizations must preserve a chain of custodianship documentation throughout the disposal process, making certain liability and traceability of disposed items.
For electronic data, utilizing software that sticks to industry standards for information cleaning is vital. This software program needs to overwrite existing information multiple times, making healing essentially difficult. It is also important to verify the performance of the information damage procedure with audits or third-party assessments.
Training staff members on safe and secure disposal practices adds another layer of safety, as human error can frequently lead to information direct exposure. Consistently reviewing and updating disposal policies makes certain alignment with evolving laws and technological developments. By executing these finest methods, companies can substantially decrease the danger of unapproved data gain access to and enhance their overall information security strategy.
Conclusion
To conclude, information devastation is a fundamental facet of computer system security solutions that makes certain the defense of confidential information from unapproved access. Carrying out reliable methods of data elimination, adhering to legal compliance, and identifying the influence on service reputation are essential components of a detailed information safety approach. By adopting finest techniques for protected disposal, organizations can cultivate depend on with customers and secure sensitive information, eventually adding to an extra secure electronic landscape.
In an age where data breaches are progressively usual, the significance of reliable data damage can not be overemphasized.Information destruction is an important part of computer system security that involves the irreversible removal a knockout post of information from storage space tools learn this here now to stop unauthorized accessibility and potential data violations. Organizations should likewise establish clear plans pertaining to data retention and devastation timelines, guaranteeing that information is not held longer than essential.
By proactively attending to legal demands, companies can alleviate threats associated with data breaches and demonstrate their commitment to information safety and security (data destruction). Ultimately, focusing on lawful compliance in data damage processes is not simply a governing commitment, but a fundamental aspect of a durable information safety technique